Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback)
Ceny a dostupnost se mohou měnit i několikrát za den. Zkontrolujte si aktuální údaje přímo v e-shopech. Všechny dostupné barvy a velikosti naleznete přímo v e-shopech.
Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback) - popis produktu
Are nuclear arsenals safe from cyber-attack? Could terrorists launch a nuclear weapon through hacking? Are we standing at the edge of a major technological challenge to global nuclear order? These are among the many pressing security questions addressed in Andrew Futter's ground-breaking study of the cyber threat to nuclear weapons.
Hacking the Bomb provides the first ever comprehensive assessment of this worrying and little-understood strategic development, and it explains how myriad new cyber challenges will impact the way that the world thinks about and manages the ultimate weapon. The book cuts through the hype surrounding the cyber phenomenon and provides a framework through which to understand and proactively address the implications of the emerging cyber-nuclear nexus. It does this by tracing the cyber challenge right across the nuclear weapons enterprise,
Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback) - související články v blogu
Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback) - další zajímavé produkty
Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback)
Are nuclear arsenals safe from cyber-attack? Could terrorists launch a nuclear weapon through hacking? Are we standing at the edge of a major technological challenge to global nuclear order? These are among the many pressing security questions addressed in Andrew Futter's ground-breaking study of

The Politics of Nuclear Weapons: New, Updated and Completely Revised (Futter Andrew)(Paperback)
This comprehensively updated second edition provides an introduction to the political, normative, technological and strategic aspects of nuclear weaponry. It offers an accessible overview of the concept of nuclear weapons, outlines how thinking about these weapons has developed and considers how
The Making of the Atomic Bomb (Rhodes Richard)(Paperback)
The definitive history of nuclear weapons and the Manhattan Project. From the turn-of-the-century discovery of nuclear energy to the dropping of the first bombs on Japan, Richard Rhodes's Pulitzer Prize-winning book details the science, the people, and the sociopolitical realities that led to the

Pakistan's Nuclear Bomb - A Story of Defiance, Deterrence, and Deviance (Abbas Hassan)(Pevná vazba)
An important book on a sensitive subject: the opacity of Pakistan's nuclear weapons

Nuclear Weapons: A Very Short Introduction (Siracusa Joseph)(Paperback)
Nuclear weapons have not been used in anger since the United States dropped atomic bombs on Hiroshima and Nagasaki in August 1945. Yet even after the Cold War, the Bomb is still the greatest threat facing humankind. As President Bill Clinton's first secretary of defence, Les Aspin, put it: 'The

Nuclear Reactions (Bell Mark S.)(Paperback)
Nuclear Reactions analyzes how nuclear weapons change the calculations states make in their foreign policies, why they do so, and why nuclear weapons have such different effects on the foreign policies of different countries. Mark S. Bell argues that nuclear weapons are useful for more than
Russian Nuclear Orthodoxy: Religion, Politics, and Strategy (Adamsky Dmitry)(Paperback)
A nuclear priesthood has arisen in Russia. From portable churches to the consecration of weapons systems, the Russian Orthodox Church has been integrated into every facet of the armed forces to become a vital part of Russian national security, politics, and identity. This extraordinary intertwining

Bytes, Bombs, and Spies: The Strategic Dimensions of Offensive Cyber Operations (Lin Herbert)(Paperback)
Offers a groundbreaking discussion of cyber weapons with a focus on their strategic dimensions. This book brings together leading specialists in the field to provide new and incisive analysis of what former CIA director Michael Hayden has called ''digital combat power'' and how the US should

Nuclear Weapons and Foreign Policy (Kissinger Henry a.)(Paperback)
In this book Professor Kissinger examines the framework of our foreign policy, the stresses to which that framework is being subjected, and the prospects for world order in an era of high international tension. The three essays were written before Professor Kissinger took leave from Harvard to

The Logic of American Nuclear Strategy: Why Strategic Superiority Matters (Kroenig Matthew)(Paperback)
For decades, the reigning scholarly wisdom about nuclear weapons policy has been that the United States only needs the ability to absorb an enemy nuclear attack and still be able to respond with a devastating counterattack. This argument is reasonable, but, empirically, we see that the US has

Blackstone's Handbook of Cyber Crime Investigation (Staniforth Andrew)(Paperback)
This authoritative Handbook provides a clear and detailed introduction to cyber crime, offering you an effective operational guide to the complexities and challenges of investigating cyber-related crimes. Written by a team of cyber crime experts, this unique book provides all police practitioners

Fallout - A Journey Through the Nuclear Age, From the Atom Bomb to Radioactive Waste (Pearce Fred)(Paperback / softback)
Social Engineering: The Science of Human Hacking (Hadnagy Christopher)(Paperback)
Harden the human firewall against the most current threats Social Engineering: The Science of Human Hacking reveals the craftier side of the hacker's repertoire--why hack into something when you could just ask for access? Undetectable by firewalls and antivirus software, social engineering relies

Bombing the Marshall Islands (Parsons Keith M.)(Paperback)
During the Cold War, the United States conducted atmospheric tests of nuclear weapons in the Marshall Islands of the Pacific. The total explosive yield of these tests was 108 megatons, equivalent to the detonation of one Hiroshima bomb per day over nineteen years. These tests, particularly Castle
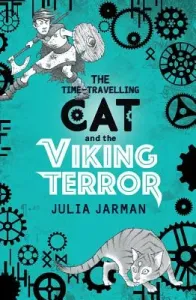
The Time-Travelling Cat and the Viking Terror (Jarman Julia)(Paperback)
Topher is planning a trip to London to visit a friend--but there have been bomb threats, which makes him worry. What's more, his beloved cat, Ka, has gone traveling again--and then, in the middle of a big bomb alert, Topher is called away--to a Saxon village threatened by Norsemen. Now he must get

History of Science: A Beginner's Guide (Johnston Sean F.)(Paperback)
From magic to the Enlightenment; Darwinism to nuclear weapons Weaving together intellectual history, philosophy, and social studies, Sean Johnston offers a unique appraisal of the history of science and the nature of this evolving discipline. Science is all-encompassing and new developments are

Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions (Gomzin Slava)(Paperback)
Must-have guide for professionals responsible for securing credit and debit card transactions As recent breaches like Target and Neiman Marcus show, payment card information is involved in more security breaches than any other data type. In too many places, sensitive card data is simply not

Nuclear Energy: An Introduction to the Concepts, Systems, and Applications of Nuclear Processes (Murray Raymond)(Paperback)
Nuclear Energy: An Introduction to the Concepts, Systems, and Applications of Nuclear Processes, Eighth Edition, provides essential information on basic nuclear physics, systems and the applications of nuclear energy. It comprehensively covers Basic Concepts, Radiation and Its Uses, and Nuclear

Oxford Playscripts: Brother in the Land (Swindells Robert)(Paperback / softback)
When a nuclear bomb wrecks his hometown and rips his family apart, 15-year-old Danny has to learn the art of survival and fast. This title offers activities designed to support the KS3 Framework for Teaching English and help students to meet the Framework objectives. Activities include work on

Weapons of the Samurai (Turnbull Stephen)(Paperback)
Featuring specially commissioned artwork, this lively study assesses the array of weapons and equipment employed by the samurai, Japan's legendary warriors. This fully illustrated new book describes and analyzes the weapons and equipment traditionally associated with the samurai, Japan's

Little Threats (Schultz Emily)(Paperback)
Both a taut whodunit and a haunting snapshot of the effects of a violent crime, Little Threats tells the story of a woman who served fifteen years in prison for murder...and now it's time to find out if she's guilty. In the summer of 1993, twin sisters Kennedy and Carter Wynn are embracing the

Nuclear Choices for the Twenty-First Century: A Citizen's Guide (Wolfson Richard)(Paperback)
An authoritative and unbiased guide to nuclear technology and the controversies that surround it. Are you for nuclear power or against it? What's the basis of your opinion? Did you know a CT scan gives you some 2 millisieverts of radiation? Do you know how much a millisievert is? Does irradiation

The Crash Palace (Wedderburn Andrew)(Paperback)
Selling Points for The Crash Palace: The author's previous book, The Milk Chicken Bomb, was longlisted for the IMPAC Dublin Literary Award and was shortlisted for the Amazon/Books in Canada First Novel Award. For fans of Willy Vlautin and Miriam Toews. Author is a musician and songwriter in the

Managing Cyber Risk (Evans Ariel)(Paperback)
Cyber risk is the second highest perceived business risk according to U.S. risk managers and corporate insurance experts. Digital assets now represent over 85% of an organization's value. In a survey of Fortune 1000 organizations, 83% surveyed described cyber risk as an organizationally complex
Hacking the Bomb: Cyber Threats and Nuclear Weapons (Futter Andrew)(Paperback) - jak nakoupit nejvýhodnější?
- Prohlédněte si také další produkty z jednotlivých e-shopů.
- Porovnejte si cenu produktu spolu s doplňkovým příslušenstvím.
- Zjistěte, zda můžete získat doručení zdarma.
- Zjistěte, zda můžete získat prodlouženou záruku nebo jiné výhody.
- Zjistěte, zda můžete získat doplňkové služby – montáž, odvoz starého spotřebiče a jiné.
- Nesoustřeďte se jen na cenu, ale na nabídku jako celek.
