Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback)
Nejnižší cena za posledních 45 dní: 1 137 Kč
ENbook.cz
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback)Ceny a dostupnost se mohou měnit i několikrát za den. Zkontrolujte si aktuální údaje přímo v e-shopech. Všechny dostupné barvy a velikosti naleznete přímo v e-shopech.
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) - popis produktu
Attacking Network Protocols is a deep dive into network protocol security from James Forshaw, one of the world's leading bug hunters. This comprehensive guide looks at networking from an attacker's perspective to help you discover, exploit, and ultimately protect vulnerabilities.
You'll start with a rundown of networking basics and protocol traffic capture before moving on to static and dynamic protocol analysis, common protocol structures, cryptography, and protocol security. Then you'll turn your focus to finding and exploiting vulnerabilities, with an overview of common bug classes, fuzzing, debugging, and exhaustion attacks. Learn how to: - Capture, manipulate, and replay packets- Develop tools to dissect traffic and reverse engineer code to understand the inner workings of a network protocol- Discover and exploit vulnerabilities such asProdukt Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) má EAN kód 9781593277505.
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) - parametry produktu
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) - historie ceny a dostupnosti
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) - další zajímavé produkty
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback)
Attacking Network Protocols is a deep dive into network protocol security from James Forshaw, one of the world's leading bug hunters. This comprehensive guide looks at networking from an attacker's perspective to help you discover, exploit, and ultimately protect vulnerabilities. You'll start
A Guide to Kernel Exploitation: Attacking the Core (Perla Enrico)(Paperback)
A Guide to Kernel Exploitation: Attacking the Core discusses the theoretical techniques and approaches needed to develop reliable and effective kernel-level exploits, and applies them to different operating systems, namely, UNIX derivatives, Mac OS X, and Windows. Concepts and tactics are presented
Packet Guide to Core Network Protocols (Hartpence Bruce)(Paperback)
Take an in-depth tour of core Internet protocols and learn how they work together to move data packets from one network to another. With this updated edition, you'll dive into the aspects of each protocol, including operation basics and security risks, and learn the function of network hardware

Applied Network Security Monitoring: Collection, Detection, and Analysis (Sanders Chris)(Paperback)
Applied Network Security Monitoring is the essential guide to becoming an NSM analyst from the ground up. This book takes a fundamental approach to NSM, complete with dozens of real-world examples that teach you the key concepts of NSM. Network security monitoring is based on the principle that

Social Network Analysis (Knoke David)(Paperback)
David Knoke and Song Yang′s Social Network Analysis, Third Edition provides a concise introduction to the concepts and tools of social network analysis. The authors convey key material while at the same time minimizing technical complexities. The examples are simple: sets of 5 or 6 entities such
Packet Guide to Voice Over IP: A System Administrator's Guide to Voip Technologies (Hartpence Bruce)(Paperback)
Go under the hood of an operating Voice over IP network, and build your knowledge of the protocols and architectures used by this Internet telephony technology. With this concise guide, you'll learn about services involved in VoIP and get a first-hand view of network data packets from the time the
Jrgen Klopp Liverpool Attacking Tactics - Tactical Analysis and Sessions to Practice Klopp's 4-3-3 (Tsokaktsidis Michail)(Paperback)
This book provides a tactical analysis of Jrgen Klopp Liverpool's 4-3-3 Attacking Tactics (70 Tactical Examples) for you the coach to learn from one of the best coaches in the world.Michail Tsokaktsidis is a UEFA 'A' Licence Coach and has used the analysis of Liverpool's attacking play to create 15

Pep Guardiola Attacking Tactics - Tactical Analysis and Sessions from Manchester City's 4-3-3 (Terzis Athanasios)(Paperback)
This book provides a tactical analysis of Pep Guardiola's 4-3-3 Attacking Tactics (56 Tactical Situations) for you the coach to learn from one of the best coaches in the world.Athanasios Terzis is a UEFA 'A' Licence Coach and has used this analysis to produce 12 Full Training Sessions (70 Practices

An Introduction to Network Programming with Java: Java 7 Compatible (Graba Jan)(Paperback)
Preface.- Basic Concepts, Protocols and Terminology.- Starting Network Programming in Java.- Multithreading and Multiplexing.- File Handling.- Remote Method Invocation (RMI).- CORBA.- Java Database Connectivity.- Servlets.- JavaServer Pages (JSPs).- JavaBeans.- Multimedia.- Applets.- Appendix A -

Diego Simeone Attacking Tactics - Tactical Analysis and Sessions from Atltico Madrid's 4-4-2 (Terzis Athanasios)(Paperback)
This book provides a full tactical analysis of Diego Simeone's 4-4-2 Attacking Tactics (73 Tactical Situations) for you the coach to learn from one of the best coaches in the world.Learn how to Attack and Counter-Attack 'from one of the best coaches in the world' with 64 Practices & Variations

Complex Network Analysis in Python: Recognize - Construct - Visualize - Analyze - Interpret (Zinoviev Dmitry)(Paperback)
Construct, analyze, and visualize networks with networkx, a Python language module. Network analysis is a powerful tool you can apply to a multitude of datasets and situations. Discover how to work with all kinds of networks, including social, product, temporal, spatial, and semantic networks
Guide to Network Defense and Countermeasures (Weaver Randy (Everst College Arizona))(Paperback / softback)
GUIDE TO NETWORK DEFENSE AND COUNTERMEASURES provides a thorough guide to perimeter defense fundamentals, including intrusion detection and firewalls. This trusted text also covers more advanced topics such as security policies, network address translation (NAT), packet filtering and analysis,

A Director's Guide to Stanislavsky's Active Analysis: Including the Formative Essay on Active Analysis by Maria Knebel (Thomas James)(Paperback)
A Director's Guide to Stanislavsky's Active Analysis describes Active Analysis, the innovative rehearsal method Stanislavsky formulated in his final years. By uniting 'mental analysis' and 'etudes', Active Analysis puts an end to the problem of mind-body dualism and formalized text memorization
Gray Hat Hacking: The Ethical Hacker's Handbook, Fifth Edition (Regalado Daniel)(Paperback)
Cutting-edge techniques for finding and fixing critical security flawsFortify your network and avert digital catastrophe with proven strategies from a team of security experts. Completely updated and featuring 13 new chapters, Gray Hat Hacking, The Ethical Hacker's Handbook, Fifth Edition explains

Nmap Network Scanning: The Official Nmap Project Guide to Network Discovery and Security Scanning (Lyon Gordon)(Paperback)
Nmap Network Scanning is the official guide to the Nmap Security Scanner, a free and open source utility used by millions of people for network discovery, administration, and security auditing. From explaining port scanning basics for novices to detailing low-level packet crafting methods used by

Web Application Security: Exploitation and Countermeasures for Modern Web Applications (Hoffman Andrew)(Paperback)
While many resources for network and IT security are available, detailed knowledge regarding modern web application security has been lacking-until now. This practical guide provides both offensive and defensive security concepts that software engineers can easily learn and apply. Andrew Hoffman,

Introducing Needs Analysis and English for Specific Purposes (Brown James Dean (University of Hawaii at Manoa USA))(Paperback / softback)
Introducing Needs Analysis and English for Specific Purposes is a clear and accessible guide to the theoretical background and practical tools needed for this early stage of curriculum development in ESP. Beginning with definitions of needs analysis and ESP, this book takes a jargon-free approach

SDN and NFV Simplified: A Visual Guide to Understanding Software Defined Networks and Network Function Virtualization (Doherty Jim)(Paperback)
A Visual Guide to Understanding Software Defined Networks and Network Function Virtualization The simple, visual, at-a-glance guide to SDN and NFV: Core concepts, business drivers, key technologies, and more! SDN (Software Defined Networks) and NFV (Network Function Virtualization) are today's

Unified Protocols for Transdiagnostic Treatment of Emotional Disorders in Children and Adolescents: Therapist Guide (Ehrenreich-May Jill)(Paperback)
The Unified Protocols for Transdiagnostic Treatment of Emotional Disorders in Children and Adolescents, based in groundbreaking research from Jill Ehrenreich-May, David H. Barlow, and colleagues, suggest that there may be a simpler and more efficient method of utilizing effective strategies, such
The Musician's Guide to Theory and Analysis Workbook (Clendinning Jane Piper)(Paperback)
This Workbook accompanies The Musician's Guide to Theory and Analysis, Fourth Edition, and features hundreds of exercises students can complete on tear-out-and-turn-in

The Illustrated Guide to Technical Analysis Signals and Phrases (Brown Constance)(Paperback)
'The Illustrated Guide to Technical Analysis Signals and Phrases 'provides traders with illustrations of more than 275 key chart patterns along with their most important variations. An innovative and soon-to-be essential addition to every technical trader's reference library, it provides: An

The Network Security Test Lab: A Step-By-Step Guide (Gregg Michael)(Paperback)
The ultimate hands-on guide to IT security and proactive defense The Network Security Test Lab is a hands-on, step-by-step guide to ultimate IT security implementation. Covering the full complement of malware, viruses, and other attack technologies, this essential guide walks you through the
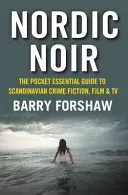
Nordic Noir: The Pocket Essential Guide to Scandinavian Crime Fiction, Film & TV (Forshaw Barry)(Paperback)
This is a compact and authoritative guide to the phenomenally popular genre of Nordic noir. The information-packed study examines and celebrates books, films and TV adaptations, from Sjowall and Wahloo's highly influential Martin Beck series through Henning Mankell's 'Wallander' to Stieg Larsson's

Text Analysis and Representation (Cushing Ian)(Paperback)
Essential study guides for the future linguist. Text Analysis and Representation is a general introduction to the methods and principles behind English linguistics study, suitable for students at advanced level and beyond. Written with input from the Cambridge Corpus, it looks at the way meaning is
Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation (Forshaw James)(Paperback) - jak nakoupit nejvýhodnější?
- Prohlédněte si také další produkty z jednotlivých e-shopů.
- Porovnejte si cenu produktu spolu s doplňkovým příslušenstvím.
- Zjistěte, zda můžete získat doručení zdarma.
- Zjistěte, zda můžete získat prodlouženou záruku nebo jiné výhody.
- Zjistěte, zda můžete získat doplňkové služby – montáž, odvoz starého spotřebiče a jiné.
- Nesoustřeďte se jen na cenu, ale na nabídku jako celek.
